Minimum requiriments for electronic signatures in Europe may disqualify perfectly valid signatures
2009-Jul-03 03:08 Filed in:All | Signatures
Various activities in Europe tries, in light of the Services directive, to establish minimum requirements for Advanced Electronic Signatures in Europe.
The background of the electronic signature directive and the electronic signature standards in Europe makes this a hard and potentially dangerous task where we run a risk of disqualifying most signature capable products for no obvious gain.
A relevant and often quoted part of the services directive is article 8, which is included here with some key phrases underlined:
Sevices directive, Article 8 - Procedures by electronic means
The standards developed at the Community level that need to be taken into account are the AdES standards developed within ETSI ESI, which are.
Analysis
A number of issues complicate this situation.
The EU signature standards are developed at the community level and are all given names that may cause one to believe that they are required to produce an Advanced Electronic Signature. This is however not the case. What is or what isn't an Advanced Electronic Signature (AdES) is defined by local national legislation in each EU member state, which has been derived from the electronic signature directive (1999/93/EC).
A major reason that the BES (Basic Electronic Signature) format of the AdES profiles by some are considered mandatory, is because they force the signers certificate to be bound to the signature, thus defending the signature against certificate substitution.
XEdES, Section 7.22 states:
The most frequent argument that suggest that protection against substitution attacks is required for a certificate to qualify as an AdES, is derived from the electronic signature directive (1999/93/EC) Article 1.
2. ‘advanced electronic signature’ means an electronic signature which meets the following requirements:
(a) it is uniquely linked to the signatory;
(b) it is capable of identifying the signatory;
Peoples that I have talked to that were part of creating the directive 10 years ago still claims that this was never the intention with the directive. The primary purpose of the signature directive was to make sure that no electronic signature was excluded from validity solely on the basis that it didn’t meet certain technical requirements. To separate signatures based on PKI from simply a fax showing a graphical image of a signature, the term Advanced Electronic Signature was invented to denote the more secure PKI based version.
While the argumentation whether these requirements from the directive requires the signers certificate to be bound to the signature or not may never end, some facts are clear:
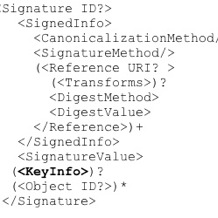
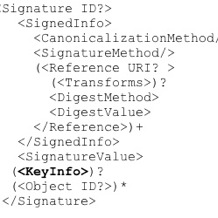
The industry standard for XML based electronic signatures, XML Dsig by W3C (http://www.w3.org/TR/xmldsig-core/) includes signature certificate information as unsigned data in the KeyInfo element.
It is important to be clear on why we would choose to disqualify XMLDsig, the most common industry standard for electronic signatures on XML based data. If the only motivation is to protect against "bad" CAs, then the rationale must be questioned. If the community accepts and trusts "bad" CAs, then we have a lot bigger problems than what can be solved by signature formats.
Here are some equally valid security issues caused by "bad" trusted CA that the XAdES BES format does NOT protect against:
It is therefore vital that the threat of bad CAs is handled on the level of supervision and accreditation of CAs rather than half-baked attempts to protect protocols against their actions at the cost of reduced international interoperability.
The "bad" CA is only an example of something that would require protection against certificate substitution attacks, but the reason that there are no other examples is most likely because there are none.
If all trusted CAs are good and well behaved then, by necessity, all certificates that can be used to validate the signature will identify the signer (and thus will fulfill the requirement of the signature directive). It is now up to the relying party, which carries the risk of acceptance, to determine if the validation certificate is adequate and sufficiently trustworthy.
A strong argument that there are no other serious threat scenario beyond the "bad" CA, is the fact that three international standard bodies independently has developed standards for signing without identifying any such threat that would motivate mandatory protection against certificate substitution.
The background of the electronic signature directive and the electronic signature standards in Europe makes this a hard and potentially dangerous task where we run a risk of disqualifying most signature capable products for no obvious gain.
A relevant and often quoted part of the services directive is article 8, which is included here with some key phrases underlined:
Sevices directive, Article 8 - Procedures by electronic means
- Member States shall ensure that all procedures and formalities relating to access to a service activity and to the exercise thereof may be easily completed, at a distance and by electronic means, through the relevant point of single contact and with the relevant competent authorities.
- Paragraph 1 shall not apply to the inspection of premises on which the service is provided or of equipment used by the provider or to physical examination of the capability or of the personal integrity of the provider or of his responsible staff.
- The Commission shall, in accordance with the procedure referred to in Article 40(2), adopt detailed rules for the implementation of paragraph 1 of this Article with a view to facilitating the interoperability of information systems and use of procedures by electronic means between Member States, taking into account common standards developed at Community level.
The standards developed at the Community level that need to be taken into account are the AdES standards developed within ETSI ESI, which are.
- CAdES (CMS based Advanced Electronic Signatures) TS 101 733
- XAdES (XML based Advanced Electronic Signatures) TS 101 903, and
- PAdES (PDF based Advanced Electronic Signatures) TS 102 778
Analysis
A number of issues complicate this situation.
The EU signature standards are developed at the community level and are all given names that may cause one to believe that they are required to produce an Advanced Electronic Signature. This is however not the case. What is or what isn't an Advanced Electronic Signature (AdES) is defined by local national legislation in each EU member state, which has been derived from the electronic signature directive (1999/93/EC).
A major reason that the BES (Basic Electronic Signature) format of the AdES profiles by some are considered mandatory, is because they force the signers certificate to be bound to the signature, thus defending the signature against certificate substitution.
XEdES, Section 7.22 states:
- 'Many current schemes simply add the certificate after the signed data and thus are subject to various substitution attacks. An example of a substitution attack is a "bad" CA that would issue a certificate to someone with the public key of someone else.'
- 'The certificate used to verify the signature SHALL be identified in the sequence; the signature policy MAY mandate other certificates be present, that MAY include all the certificates up to the point of trust.'
- 'This is a signed property that qualifies the signature.'
The most frequent argument that suggest that protection against substitution attacks is required for a certificate to qualify as an AdES, is derived from the electronic signature directive (1999/93/EC) Article 1.
2. ‘advanced electronic signature’ means an electronic signature which meets the following requirements:
(a) it is uniquely linked to the signatory;
(b) it is capable of identifying the signatory;
Peoples that I have talked to that were part of creating the directive 10 years ago still claims that this was never the intention with the directive. The primary purpose of the signature directive was to make sure that no electronic signature was excluded from validity solely on the basis that it didn’t meet certain technical requirements. To separate signatures based on PKI from simply a fax showing a graphical image of a signature, the term Advanced Electronic Signature was invented to denote the more secure PKI based version.
While the argumentation whether these requirements from the directive requires the signers certificate to be bound to the signature or not may never end, some facts are clear:
- In many systems and environments it is possible to derive and prove with reasonable degree of certainty who the signer is, even if the certificate used to validate the signature is not signed by the verified signature.
- The basic PKI technology used to create and validate signatures depends on trust in certification authorities (CAs). Most security properties fail if the relying party chooses to trust a "bad" CA. To date there are no security architectures that can claim to securely deploy PKI, which safely mitigate threats caused by relying party trust in "bad" behaving CAs.
The industry standard for XML based electronic signatures, XML Dsig by W3C (http://www.w3.org/TR/xmldsig-core/) includes signature certificate information as unsigned data in the KeyInfo element.
It is important to be clear on why we would choose to disqualify XMLDsig, the most common industry standard for electronic signatures on XML based data. If the only motivation is to protect against "bad" CAs, then the rationale must be questioned. If the community accepts and trusts "bad" CAs, then we have a lot bigger problems than what can be solved by signature formats.
Here are some equally valid security issues caused by "bad" trusted CA that the XAdES BES format does NOT protect against:
- The signer is the attacker and signs with the certificate from the "bad" CA. Here the XAdES profile will even help the attacker to convince relying parties to rely on the "bad" certificate.
- The "bad" CA simply creates a whole new faked message and signs it with a new key pair for which the "bad" CA has issued a convenient attack certificate
It is therefore vital that the threat of bad CAs is handled on the level of supervision and accreditation of CAs rather than half-baked attempts to protect protocols against their actions at the cost of reduced international interoperability.
The "bad" CA is only an example of something that would require protection against certificate substitution attacks, but the reason that there are no other examples is most likely because there are none.
If all trusted CAs are good and well behaved then, by necessity, all certificates that can be used to validate the signature will identify the signer (and thus will fulfill the requirement of the signature directive). It is now up to the relying party, which carries the risk of acceptance, to determine if the validation certificate is adequate and sufficiently trustworthy.
A strong argument that there are no other serious threat scenario beyond the "bad" CA, is the fact that three international standard bodies independently has developed standards for signing without identifying any such threat that would motivate mandatory protection against certificate substitution.